Identifying Email Phishing Attempts
DoIT does everything it can to keep annoying and dangerous phishing emails out of your inbox; however, a few do get through. Below are six clues to watch for when determining whether an email message is a phishing attempt, so we each do our part to help promote a safe computing environment at Stony Brook University.
If you suspect an email is a phishing attempt, forward it to phishbowl@stonybrook.edu and use built-in Gmail tools to report it.
Clue #1: Vague "From" Field/Subject Line
If you see all caps and notice that there is no name or official department in the "From" field, this is a pretty good indicator that the message you've just received is a phishing attempt. Also, in this example, notice the return email address is allegedly from NYU (it's not really) and the "Subject" line is quite vague. Legitimate emails usually have more informative subject lines.
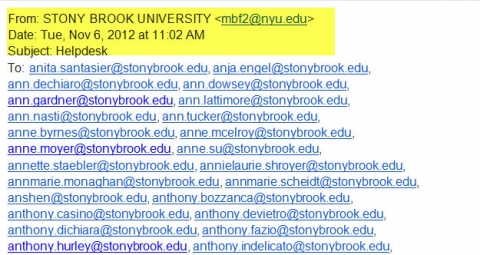
Clue #2: Strange "To:" List
It's a bad sign when the distribution list is long and alphabetical (see example above) or the email message is addressed to absolutely no one (see example below):
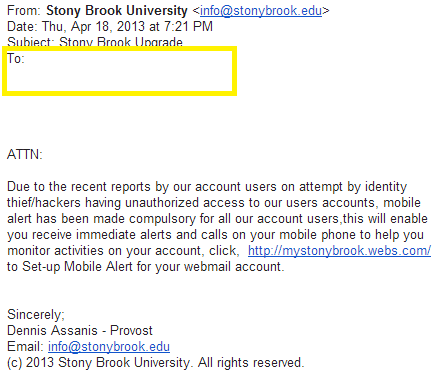
Clue #3: Missing Salutation
Legitimate email messages typically include formal salutations to individuals, groups, or departments (not ATTN:)
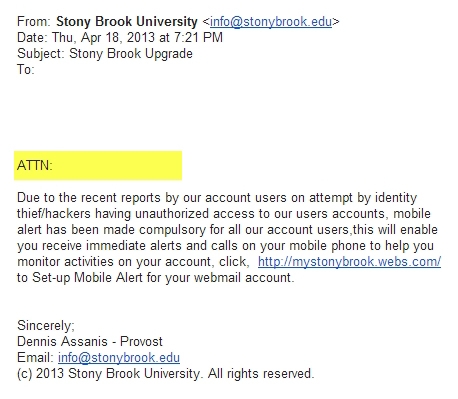
They will seldom use an exclamation point in the salutation, let alone three!
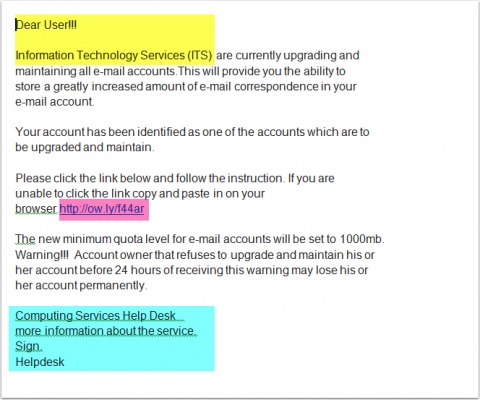
Clue #4: Incorrect Names/Non-Existent Departments
You can tell the message above is a scam because it uses the wrong name. At Stony Brook, the IT department is called the Division of Information Technology (DoIT), not Information Technology Services (ITS). Like the NYU address above, you can tell this is a template that spammers use. Look for acronyms or organizational oddities that are out of place.
Clue #5: Poor Grammar/Spelling
Poor grammar and punctuation in the body of the message is usually a sure sign that you've received a phishing email. The run-on sentence in the example below that doesn't make any sense at all and surely wasn't drafted by our Provost or his staff is something to watch for. The inappropriate use of commas, the lack of spaces, and the semicolon in the closing are also indicators. Titles are also a contextual clue "Provost and Senior Vice President for Academic Affairs" is the norm. Be on the lookout for inappropriate uses of the copyright symbol, too. Stony Brook's Provost would never copyright his email messages. While messages are composed by humans which means on occasion mistakes will be found, no senior staff member at Stony Brook would ever send such a poorly-crafted message.
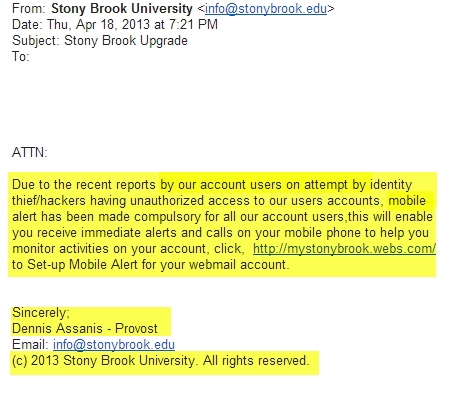
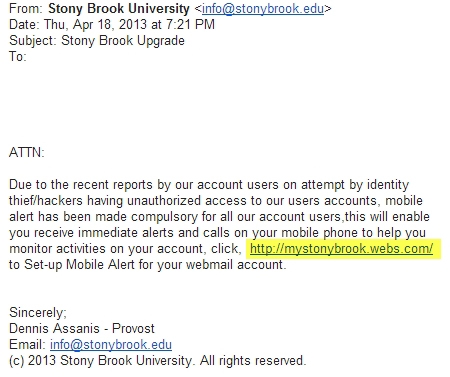
Clue #6: Generic/Strange Links
Most important! - Treat any and every link that does not end in stonybrook.edu with great suspicion. The link provided above in pink is so generic, it practically screams phishing scam. You can tell the one below is fraudulent because it is not on the stonybrook.edu domain and actually ends in ".com." Websites hosted by institutions of higher education typically end in ".edu." Business websites end in ".com." Never click on suspicious links. If you have the slightest inkling of doubt, call to verify.
Still not Sure?
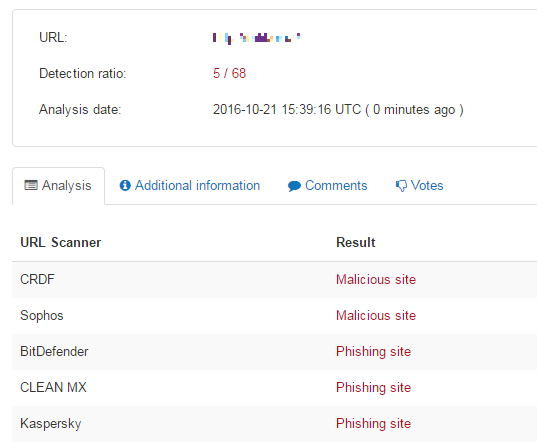
If you think you might've received a phishing email - but you're still not sure - you can check the link
- Launch the Virus Total Link Scanning Tool
- Click on URL
- Copy and paste the link from your email
- Click on Scan it!
- Once your scan is complete, you'll receive this message
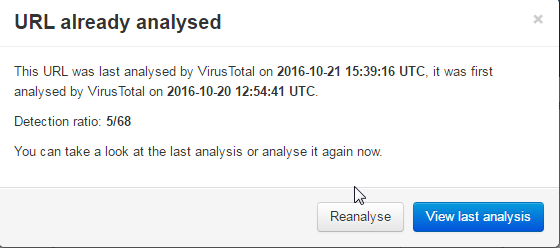
- If the detection ratio is 0, click on Reanalyze, otherwise click on View Last Analysis
- The page that opens will list what vendors detected this site as malicious/phishing - you should avoid anything with a detection ratio that's not 0